Outsourcing Benefits and Ways to Mitigate Possible Risks

Outsourcing is the common practice of contracting out business functions and processes to third-party providers. The benefits of outsourcing can be substantial – from cost savings and efficiency gains to greater competitive advantage. Both well-established companies and startups reveal that outsourcing is beneficial for them.
On the other hand, loss of control over the vendor is often a potential business risk associated wih outsourcing. You should carefully consider the advantages and disadvantages of outsourcing before deciding whether to contract out any activities or business operations. So, let’s finally consider the benefits and risks of outsourcing.
Listen to “Outsourcing Benefits and Ways to Mitigate Possible Risks” on Spreaker.
Benefits of Outsourcing
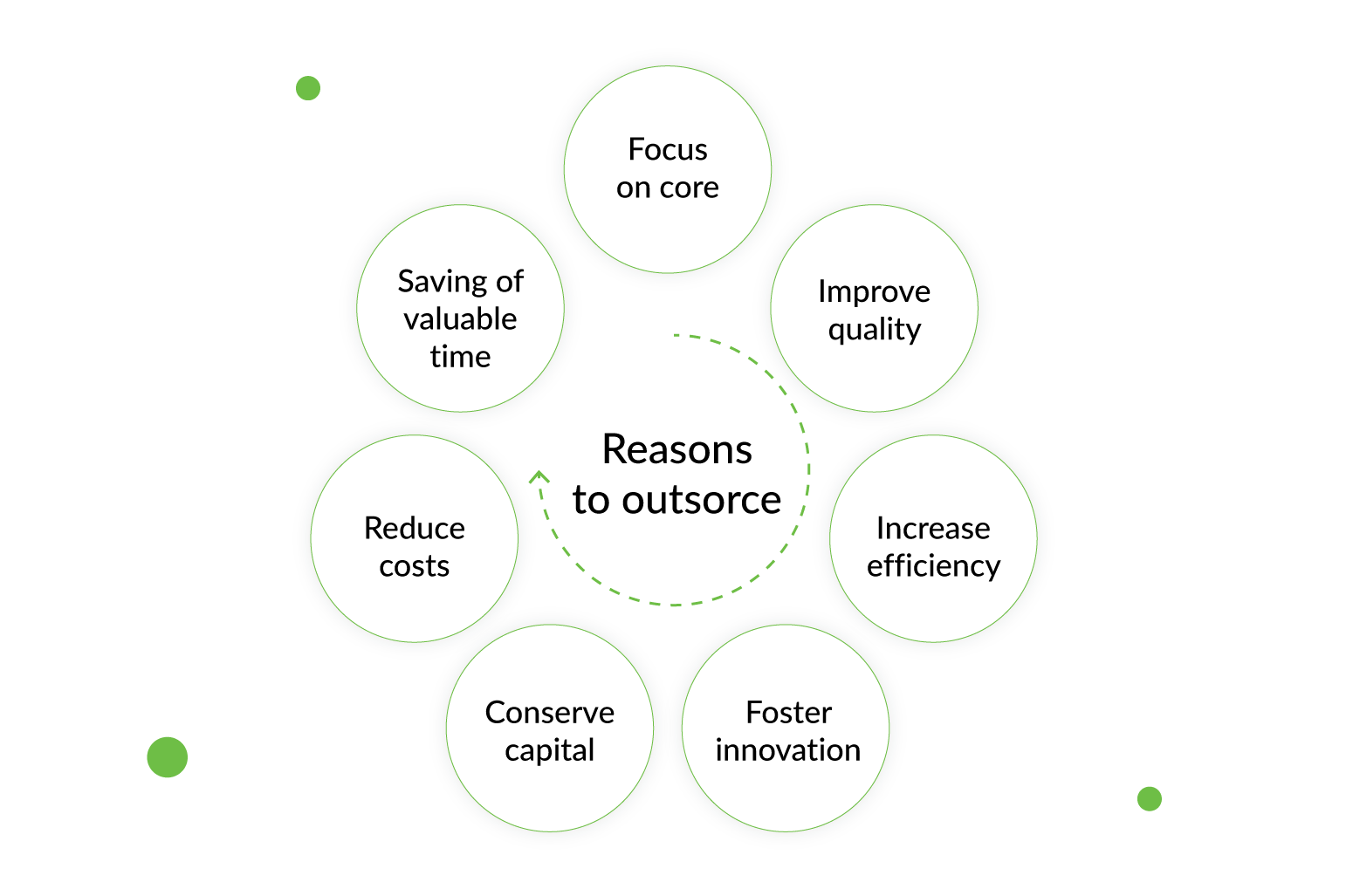
According to the statistics, most US businesses (66%) outsource at least one department. Meanwhile, many small businesses, around 37%, outsource to stay competitive. There are many reasons why a business may choose to outsource a particular task, job or a process. For example, some of the recognized outsourcing benefits include:
- improved focus on core business activities – outsourcing can free up your business to focus on its strengths, allowing your staff to concentrate on their main tasks and on the future strategy.
- increased efficiency – choosing an outsourcing company that specializes in the process or service you want them to carry out for you can help you achieve a more productive, efficient service, often of greater quality.
- controlled costs – cost-savings achieved by outsourcing can help you release capital for investment in other areas of your business.
- increased reach – outsourcing can give you access to capabilities and facilities otherwise not accessible or affordable.
- greater competitive advantage – outsourcing can help you leverage knowledge and skills along with your complete supply chain
This is a far from complete list of outsourcing advantages, but these are the ones worth paying attention to.
Read More: The CTO Dilemma: Building an Inhouse Team vs. Finding a Technical Partner
Risks of Outsourcing and How to Mitigate Them
However, IT outsourcing projects are not an easy task to manage and many projects fail even though a lot of research exists within the area.
Many of the risks of outsourcing of sotware development can be mitigated with solid preparation and planning, but nothing helps more than understanding what the potential pitfalls are, and how they might be avoided.
We’ve selected the most common concerns you may have about outsourcing IT and explained the best practice to managing the risks of IT outsourcing. Hopefully, our tips will help you cast all your doubts aside.
So, what are the common things to pay attention to?
Risk 1: The Issue of Trust
If you are at the stage of considering whether outsourcing business processes is a good idea, how you can trust someone located thousands of miles away has also probably crossed your mind. The degree of this trust depends on how many points an outsourcing company can score as a result of risks analysis and whether these risks can be reduced. Verifying these with an outsourcing company that you’d like to make your future partner can give you near accurate predictions on your endeavour outcome.
Solution:
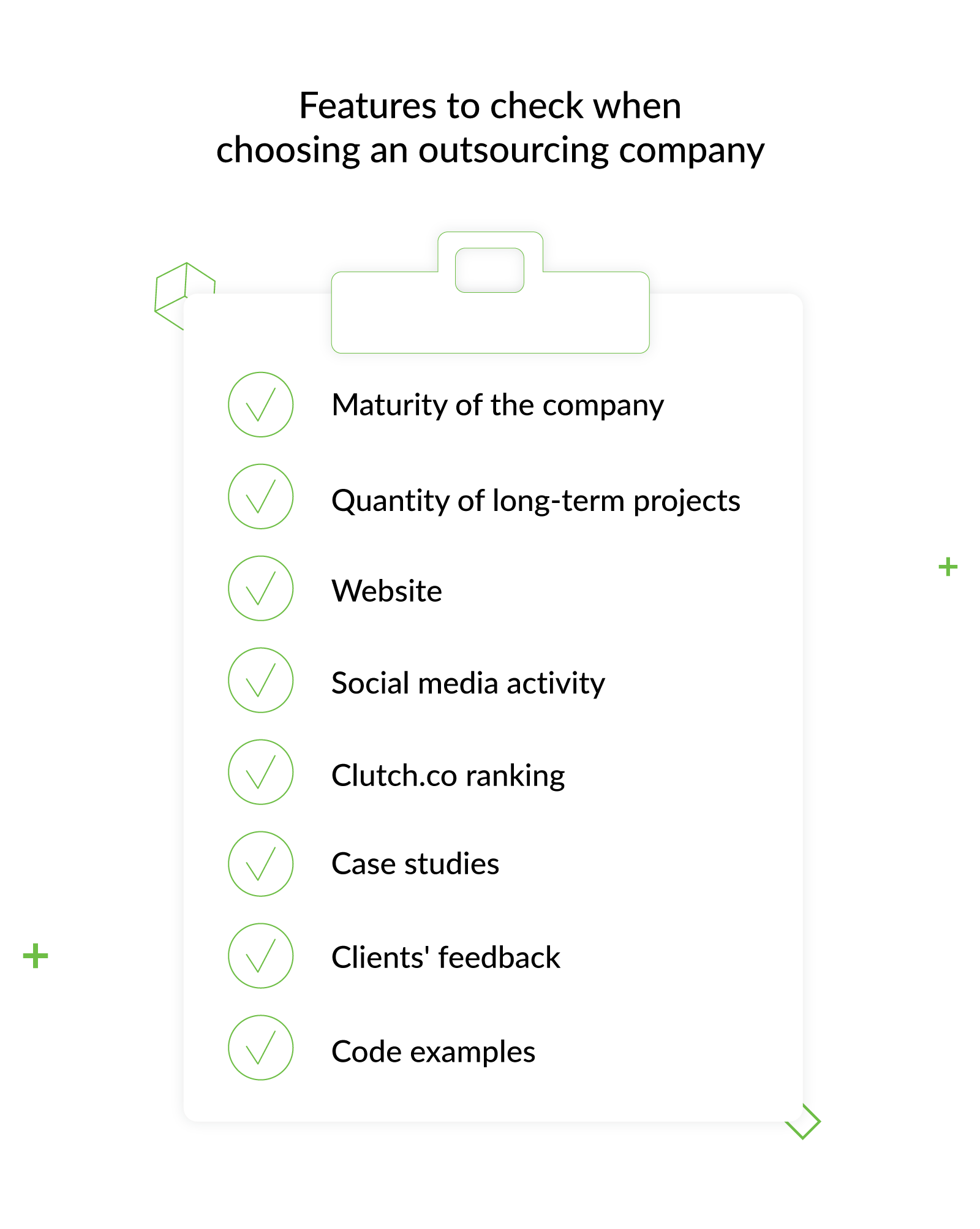
Choose the company based on the following:
- The maturity of the company: for how long is the company presented on the market, the average project size, the quantity of the employees, etc…
- The quantity of the long-term projects/clients and the amount of successful projects – for the past year
- The company’s website. Why would these guys make something valuable for you if they are not able to create something valuable for themselves?
- Company’s social media activity. An IT provider’s will to share its knowledge and its inner life with society is always a good sign.
- The knowledge sharing process and technical skills development inside the company and the company’s participation in the global events.
- Take a look at the company’s ranking on independent review platforms such as Clutch.co
- Case studies. These include client overviews, history of the cooperation, problems the client wanted to solve, challenges that appeared, the solution itself, and the technology stack used.
- Get feedback directly from clients (current and past). Old clients are especially important to speak with because they have nothing to lose by telling the truth. However, do not forget that all of them are business people perhaps busy nurturing their projects, and the response time can be varied.
- If possible, make an on-site visit to validate your “compatibility” — you’ll need to cooperate with these people in future. Discuss the project related topics with those in the office directly.
- Asking for a code example used to implement some functionality in previous projects won’t be a bad idea. In such a way you can check the syntax, how the code is written and the best practices used in it.
Risk 2: Domain Expertise
Further vital criterion that should shape your opinion about an outsourcing IT company is its domain expertise; that is, the area of professional skills and development. As a rule, companies provide information on certification and many are certified to high-grade quality standards. The backgrounds (such as experience and degrees) of your vendor team are equally important.
Solution:
Find out the technologies the selected vendor is proficient in, have a look at its implemented projects, and quantify and qualify its accomplishments.
Risk 3: Lack of Expertise with Remote Teams
Pretty often clients say they are not ready to outsource or hire remote teams or that they need to have all staff based locally. This mostly happens if the company’s founders have no experience in outsourcing and managing remote IT operations. Such a situation may become catastrophic if you choose an amateur service provider. Clearly, you don’t want vendors to get their first remote work experience when cooperating with you.
Solution:
Choose a company with a well-established model for remote team integration. Having this model in place proves that a vendor has the needed experience and skills required for successful collaboration.
Additionally, your potential partner should be able to provide training sessions and consultation regarding all the aspects of remote work.
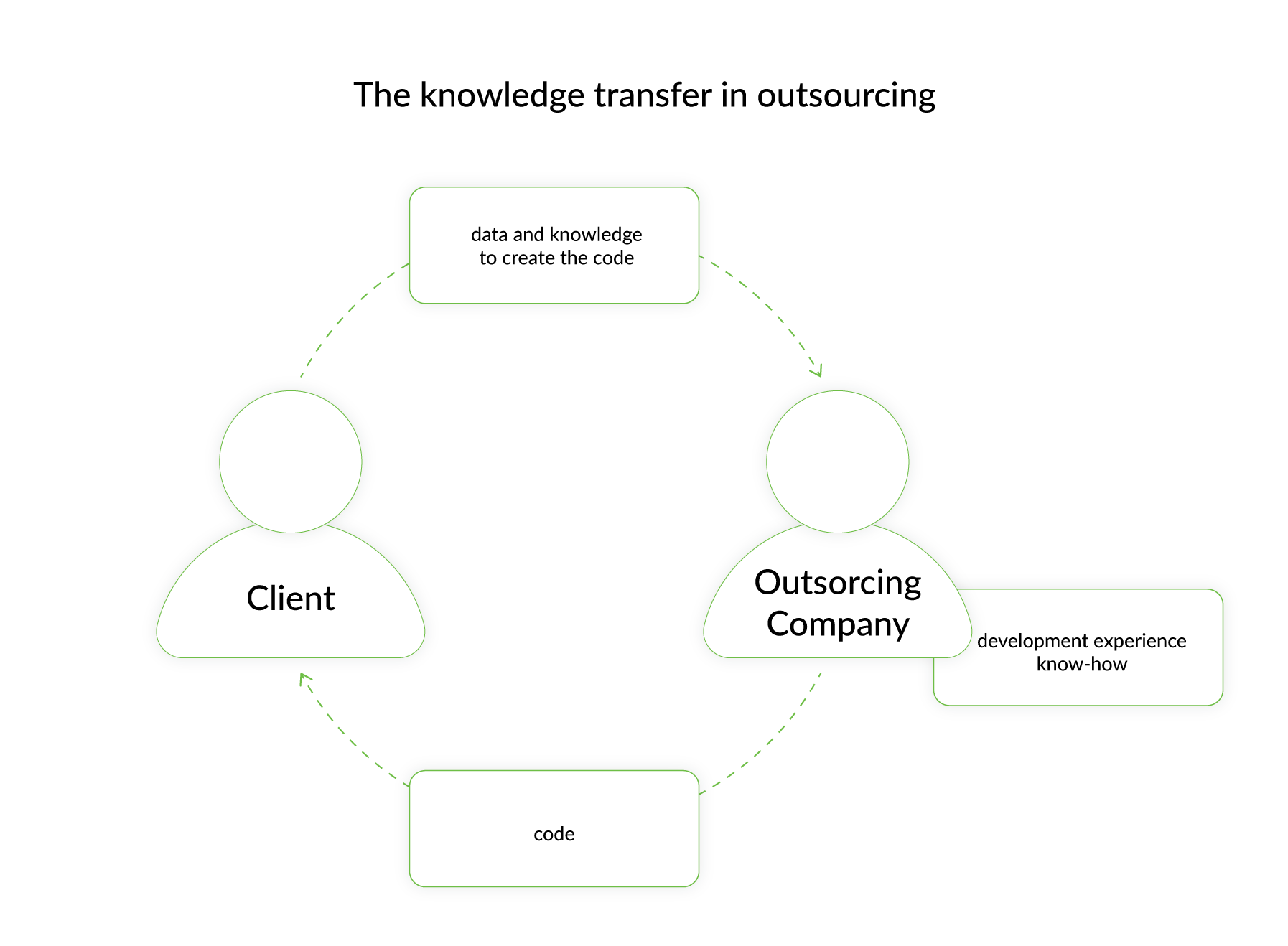
Risk 4: Knowledge Transfer
One of the most crucial factors influencing the success of an IT outsourcing relationship is knowledge transfer.
In the most basic form of outsourcing, there are two types of knowledge transfer. The first one is from the company that wants the outsourcer to produce something. And here it is essential to provide all the information, data and knowledge in order to ensure that the outsource company can deliver what you want. The second one is that the “know-how” and fluency in the developed product is not “owned” by the customer. The code is “owned” but not the know-how/experience.
So, a successful outsourcing project is a two-way street that requires a smooth flow of knowledge transfer in both directions.
Solution:
- When it comes to technology, look for outsourcers that have moved beyond manual information capture and have state-of-the-art software tools that capture business processes. This ensures that the knowledge transfer occurs accurately, quickly and efficiently.
- It is also important to select outsourcers that are always on the lookout for the latest knowledge transfer technologies. Adopting an effective technology policy will bring great dividends to the company and help in meeting cost targets.
- Finally, look for an outsourcer that can create an innovation roadmap as part of the knowledge transfer process. This demonstrates the provider’s ability and depth of knowledge in a specific domain in order to optimize and run your operations and will provide both immediate and long-term benefits.
Risk 5: Confidentiality and Intellectual property
When you outsource, you delegate part of your IT infrastructure to another company. In doing so, you hand over sensitive information such as processes, employees’ details and other important data to the outsourcer. So, it is natural that you may worry about the way the outsourcing provider handles your resources security.
Solution:
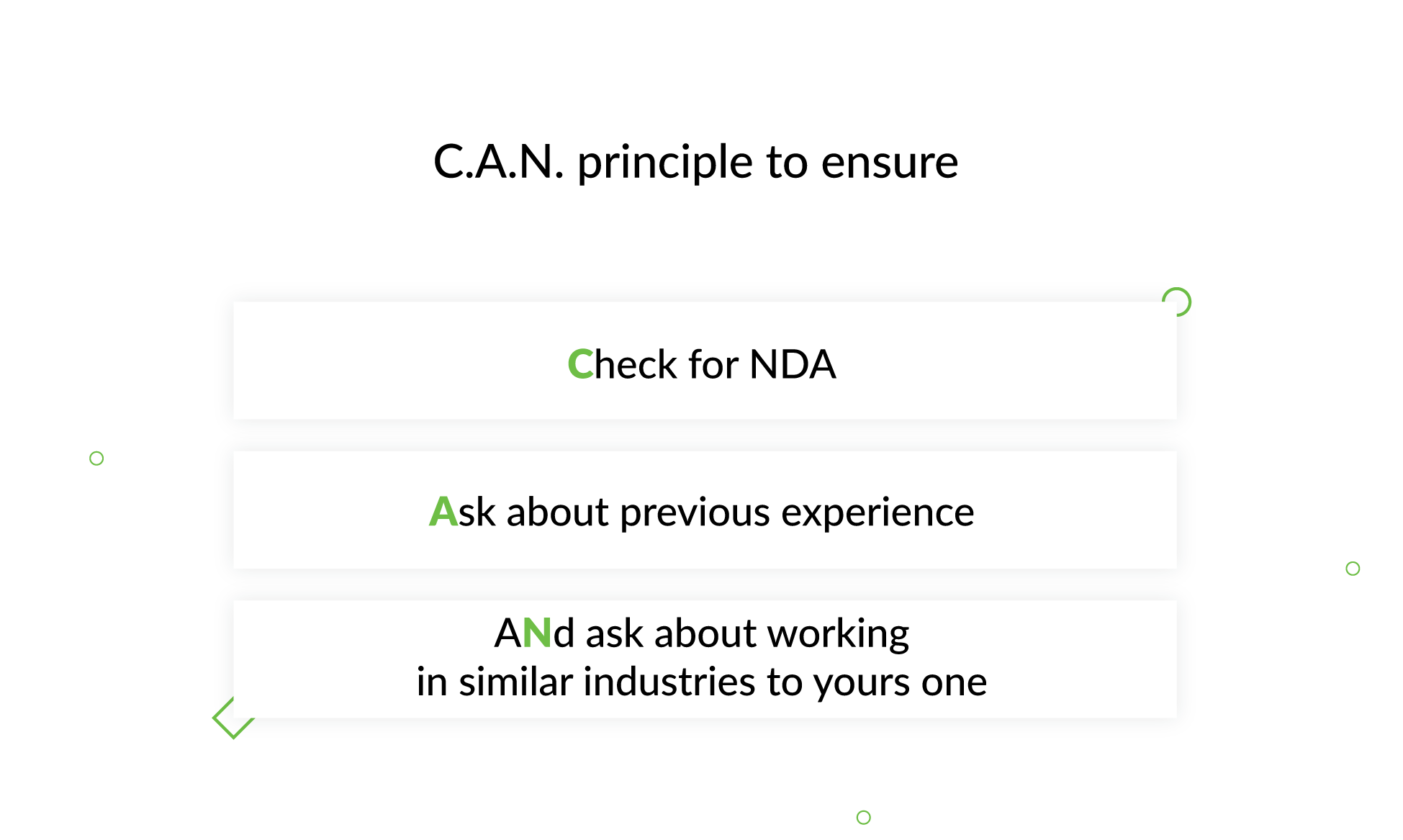
Selecting an IT company working in compliance with international security standards can dispel your concerns about security. To help you find a reliable outsource company try using (C.A.N):
- Check if the company is open to signing up for NDA (Non-Disclosure Agreement),
- Ask if the company has any previous experience in working with sensitive data
- aNd if they have completed any projects in the industries similar to the one you work in
Also, include all the necessary clauses regarding the safeguard of proprietary rights and confidentiality in the service-level agreement.
Risk 6: Hidden and Uncertain Costs
This is another risk of outsourcing services. Just imagine you have outsourced IT to lower your cost, but the vendor creates new overheads for changes, modifications and adaptations during the service period. Your overall outsourcing cost is bound to skyrocket this way. It has been found that hidden costs in outsourcing add an average of 25% to the price of engagement..
Solution:
- Identify your current IT needs and also factor in the future needs if you are planning to scale up or down. This will help you to negotiate the right cost with the service provider.
- IT outsourcing is worth your investment as long as you conduct a thorough risk assessment at the beginning, followed by a close monitoring during and after the implementation.
- Make sure the contract includes a full list of additional expenses that may occur, like the purchase of software and hardware for your team, overtime, and after-hours communication.
- Engage a third-party law firm for guidance if your personnel lack expertise and need advice on the contract.
Risk 7: Quality of Service
One of the main reasons to outsource is the expectation of receiving a better service from the outsourcer than from internal staff. In order to not be disappointed with the dedicated team skills, stick to the following
Solution:
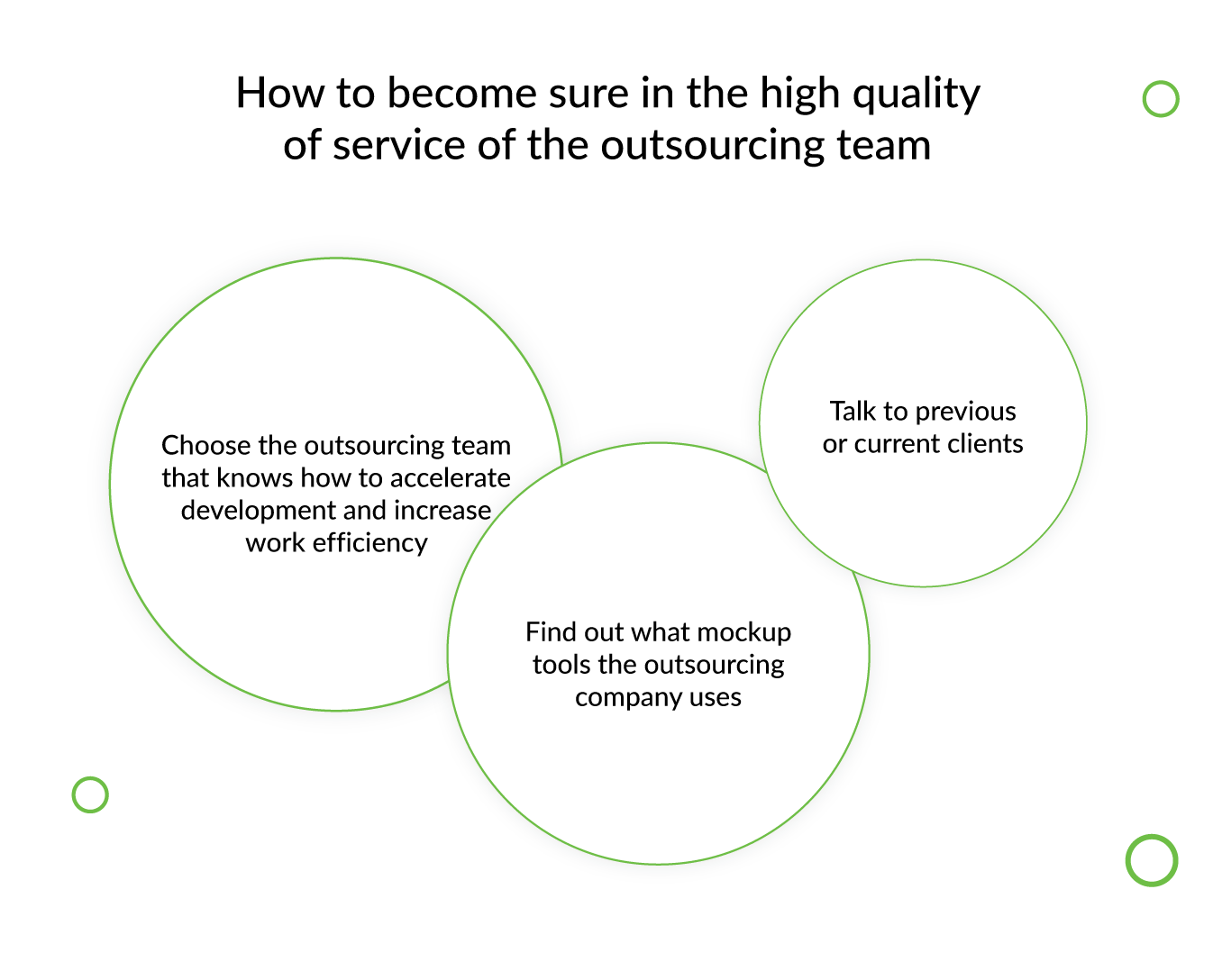
- Choose an outsourcing team based not only on their technology skills but also their ability to apply useful tools and frameworks that accelerate development and increase work efficiency and productivity.
- Figure out what mockup tools, delivery process/methodology, tracking systems, and quality software metrics the vendor employs to make software, and discuss your expectations with the vendor.
- Talk to past or current clients. Past clients are especially important since they have nothing to lose by telling the truth. Learn what it’s like to work with the provider, the difficulties you might face, and how you might expect the final product to turn out.
Read More: Why You Need QA and How It Can Save Your Money
Risk 8: Loss of Control over the Process
Hiring an outsourcing firm to build software for you typically means ceding control of, and thus insight into, the development process. This might not be that big of a deal if the work you’re outsourcing isn’t cored to your business. Otherwise, this lack of control could cost you time and money.
Solution:
Start from improving communication and discussing all the points of your cooperation. Then, make sure that your vendor uses special requirement-tracking software, where you can make changes and add new points even when the work is in progress. Finally, establish regular reporting, i.e. daily or weekly, depending on the complexity of your project. And, if you want “to feel the pulse” of your remote team as if it sits in the next room, choose the Dedicated Development Team outsourcing model for long term projects – you will be able to directly manage and control every employee.
Risk 9: Viability of Service Provider
Perhaps the worst nightmare facing the customer of outsourcing firms is the prospect that the provider will fail and leave customers in the lurch without access to critical services and systems.
Solution:
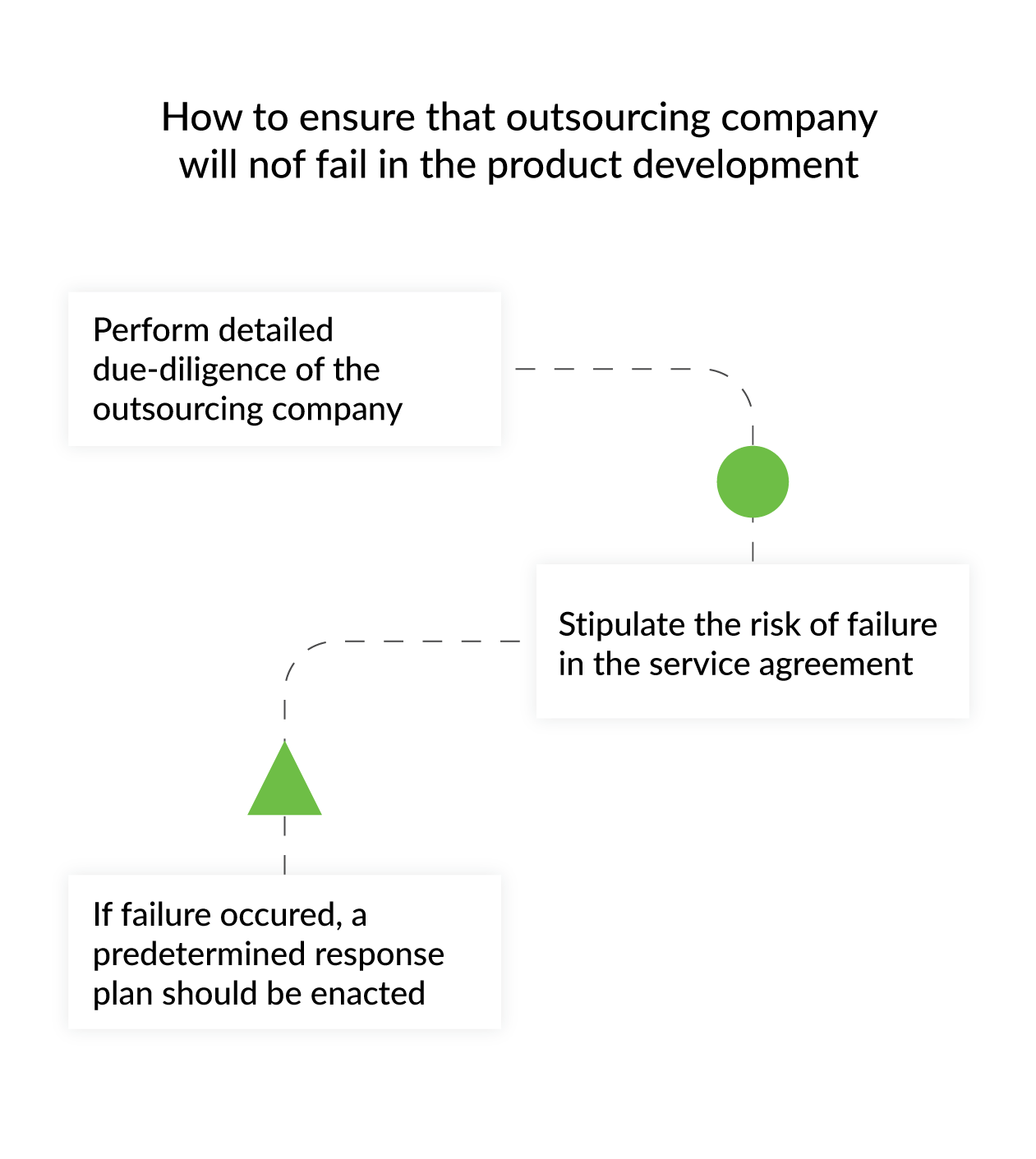
In order to reduce the risk, it is important that customers follow a clear and structured approach to minimize the chance of being subjected to such a failure or to reduce the impact if such a failure does occur. Before entering into a service-provider arrangement, the prospective purchaser of the services should perform a complete and detailed due diligence process.
Additionally, the agreement between the customer and outsourcer should anticipate the potential failure of the service provider and include provisions for such an event. These provisions should include a set of contingency plans allowing the customer organization to avail itself of alternative facilities and resources or to take over the resources of the outsourcer that have been applied to the customer’s particular service. The operational contingency plans need to be exercised and rehearsed on a regular basis to ensure that they will work.
At the time of failure, a predetermined response plan should be put into effect to protect the outsorcer’s customers from the negative aspects of such a failure, which might affect negotiations with other vendors.
Risk 10: The time zone difference
When working with an outsourcer, a time zone difference may become an obstacle if not handled correctly. It’s not a problem if the time zone difference is a couple of hours. But when it constitutes 6-7 hours, something that amounts to a whole business day, collaboration with the development team may be shifted.
Solution:
The time zone obstacle can be overcome by using processes and technologies to empower people to engage, connect and collaborate. It is also important to give the team a common working space to share, find, and collaborate on the information they need to get the work done.
Also, the time zone difference gives the benefit of “follow the sun” working model, in which the offshore team takes on work in the client’s night time and returns the result in the next day’s morning.
Summing up
As you can see, the outsourcing benefits and risks can be very diverse. Fortunately, the outsourcing risks highlighted above can be easily averted when the team selection and development outsourcing are thoroughly planned.
Preparations may be tedious at times, but the outcome should come close to meeting your expectations, especially when you choose to hand over the work to agile teams. With the right plan, you’ll be equipped to address even the gravest software development risks so that your customer-vendor relationships can bring positive results and make your outsourcing experience beneficial.
If you are looking for a reliable team for outsourcing software development, contact DjangoStars.
- How to mitigate outsourcing risks?
- Nothing helps more than understanding, what the potential pitfalls are, and how they might be avoided. Many risks of outsourcing software development can be averted or mitigated with solid preparation when the team selection and development outsourcing are thoroughly planned.
- Is it possible to lose control in software development outsourcing?
- Loss of control over the vendor is often a potential business risk associated with outsourcing. Hiring an outsourcing firm to build software for you typically means ceding control of, and thus insight into, the development process. This might not be that big of a deal if the work you’re outsourcing isn’t cored to your business. Otherwise, this lack of control could cost you time and money. You should carefully consider the advantages and disadvantages of outsourcing before deciding whether to contract out any activities or business operations.
- Which of the advantages of outsourcing have you experienced firsthand?
- There are many reasons why a business may choose to outsource a particular task, job, or process. For example, some of the recognized benefits of outsourcing include:
- improved focus on core business activities,
- increased efficiency,
- controlled costs,
- increased reach,
- greater competitive advantage.
- Do these advantages and risks of outsourcing relate only to software development?
- Business outsources not only software development. According to a survey, 90% of U.S. companies consider outsourcing crucial to their growth. Meanwhile, 78% of new and small companies think outsourcing gives them a competitive advantage. Thus, every company that uses outsourcing should be aware of its main benefits and risks.
- Can I outsource the development of my project to you?
- The DjangoStars team has over 13 years of software development expertise. If you want to make the development of your project more productive, high-quality, and efficient, it's a great idea to contact us for a consultation.









Всего комментариев: 0